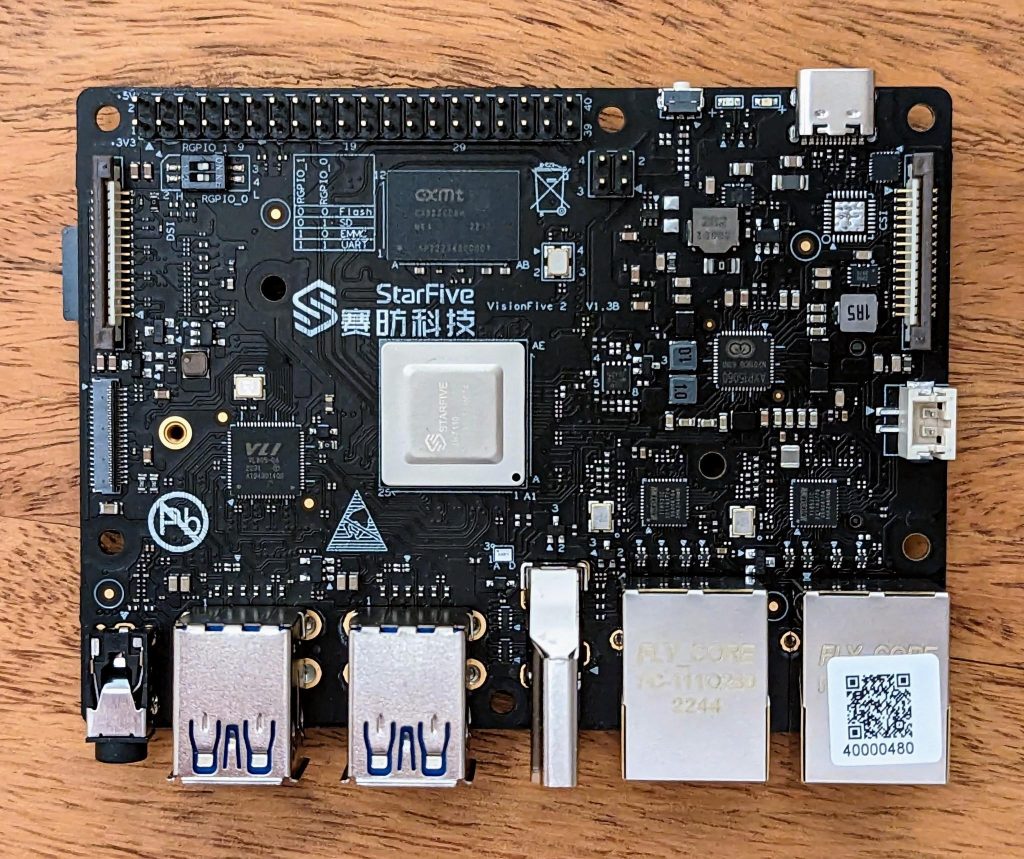
In March, I wrote about my initial contact with the StarFive VisionFive 2 board. Since then, StarFive released a couple of new releases of their Debian-based operating system. However, these releases are still based on a Debian unstable snapshot from 2022 and a Linux 5.15.0 kernel that contains several severe vulnerabilities. Updating the image is not possible without breaking their custom fixes to mesa.
By now there are also dozens of distributions available for the board. Many of them rely on StarFive’s outdated kernel sources. Others merge those kernel sources with more recent upstream patches or selectively apply StarFive patches on up-to-date mainline kernel sources. However, looking at the current status of the upstreaming efforts for the JH7110 SoC, it shows that most parts of the SoC are supported in mainline Linux 6.6. The most important part missing is certainly the HDMI output.
As I am using the board purely headless, i.e., without any display, HDMI does not matter for me. With that, openSUSE Tumbleweed looked very interesting to me, currently coming with a stock Linux 6.6-rc3 kernel and stock u-boot 2023.10-rc4 and promising regular, rolling updates. However, it comes with several issues, namely:
- It boots up with 8 GiB of memory visible to the kernel – no matter how much memory your board has. If you have less than 8 GiB, segmentation faults will bite you.
- Lots of hardware that should work with the supplied kernel does not. For example, PCIe, USB, thermal sensors, SPI, etc…
- It feels slow, in particular when I/O on the SD card is involved.
- It does not properly shutdown. Instead, in most cases, the board freezes on shutdown and the file systems need a check on next boot.
By now I could fix most of these issues. If you are interested or affected yourself, read through the solutions / workarounds below.
Read More